If you’re looking for the most private email provider, adding a custom domain should be a key part of your checklist. Domains enhance your privacy with greater ownership, portability, and aliasing to make sure you stay secure in all email communications. Read more
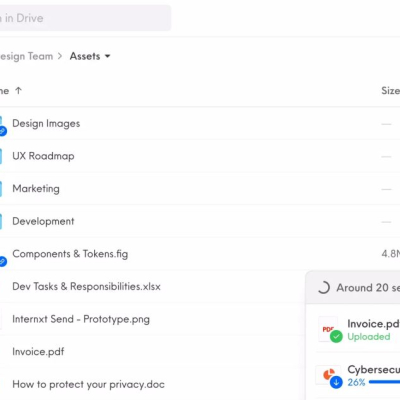
Let me introduce you to Internxt, a great alternative to Google Drive, Dropbox, WeTransfer and Google Photos. Read more
If you're looking for a Gmail or Google Workspace alternative, then Skiff products might catch your interest. Read more
The world and its borders are slowly opening up after strict Covid lockdowns, and people are looking forward to travelling again. While this is great and fun, keep in mind that you might be subject to random searches and highly invasive and traumatic experiences. Read more
I want to introduce you to a great Android developer team that released countless alternatives to apps that usually come for free but invade your privacy. Read more
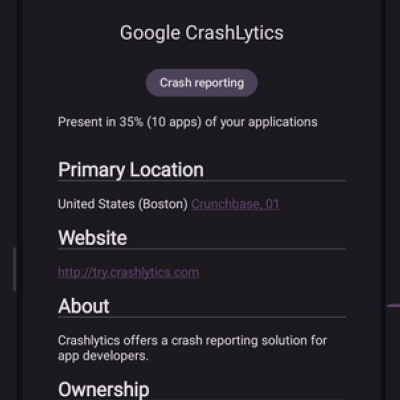
Today, I want to shed light on a fairly unknown but powerful Android app that helps you to locate trackers embedded in all your smartphone apps. Read more
The security team of the popular password manager LastPass can't seem to catch a break. This is the second security breach this year, and they are connected. Read more
Apple Inc. has limited the AirDrop wireless file-sharing feature on iPhones in China after the mechanism was used by protesters to spread images to other iPhone owners. AirDrop allows the quick exchange of files like images, documents, or videos between Apple devices. Read more